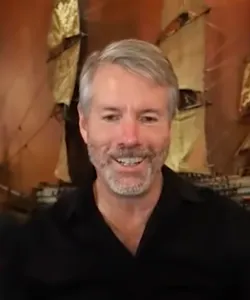
Although Saylor has been publicly critical of Ethereum, that didn't seem to raise flags among those eager to receive an airdrop of the Ethereum-based "MSTR" token that the company's Twitter account claimed they had just launched. Those who fell for the phishing link were redirected to a website that spoofed the real MicroStrategy website, with malicious code that drained funds.
Around $440,000 was stolen thanks to the fake announcement, with the majority of it coming from one wallet that was drained of a variety of tokens notionally worth around $425,000.