The Blockchain Group is behind a number of different services, including a crypto wallet called Eniblock and an open source software bounty project called Bountysource. Users of the Bountysource project have been complaining about issues receiving payments since as far back as May 2023.
The Blockchain Group suspends stock trading in apparent financial crisis
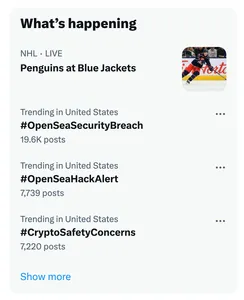
Network of fake Twitter accounts impersonating crypto security firms phish panicked victims
According to researcher zachxbt, who himself was one of the impersonated, the scammers have stolen more than $300,000 in various assets using this technique.
This is not the first time such a technique has been used — a scammer attempted a similar, though less successful, scheme in April 2022. Scams like this take advantage of the poor UX in the crypto world for tracking and revoking wallet permissions that have been granted, requiring people to use third-party websites created for this purpose. Some of them are legitimate, but there are many malicious copies of these revocation sites that prey upon users who may be acting quickly in fear that their assets are at risk.
Up to $1 billion stored in early Bitcoin wallets may be at risk due to "Randstorm" vulnerability
Unciphered worked with various wallet providers to contact people whose wallets may be vulnerable, though ultimately it is up to those wallet holders to secure their funds by creating new wallets and transferring their tokens. Unciphered also noted that some Dogecoin, Litecoin, and Zcash wallets may be vulnerable due to shared code.
Wallet drainer steals more than $60 million in six months
CREATE2 to generate new addresses for each malicious signature. This allows the drainer to sidestep security alerts built into some crypto wallet software that would flag known malicious addresses.ScamSniffer identified one victim who lost almost 17,000 GMX (~$927,000) to this drainer after signing a malicious transaction.
Wallet linked to Binance deployer loses $27 million in apparent hack
Crypto researcher zachxbt observed that the wallet targeted for the theft had in 2019 received a transfer from the Binance deployer, suggesting that the compromised wallet may have some ties to Binance itself.
Raft exploited for $3.3 million, then hacker screws up
The attacker then went to convert the R into ETH, which they would then be able to launder and cash out. However, an error in the attacker's code caused 1,570 ETH ($3.25 million) to be sent to the burn address, rendering it permanently inaccessible to everyone including the hacker. Only 7 ETH remained. However, because they had to spend ETH to fund the attack, the hack ultimately resulted in a loss of 4 ETH (~$8,000) for the perpetrator. Oops.
As a result of the hack, the R stablecoin lost its dollar peg, plummeting down to around $0.70. Raft acknowledged the attack and announced that they had paused minting.
Samudai treasury drained
Agarwal sent a message to the thief shortly afterwards, offering a 10% "bounty" in exchange for the return of the rest of the funds. The attacker didn't seem to be interested, and in mid-January began tumbling the assets through the Tornado Cash cryptocurrency mixer.
Samudai didn't seem to publicly acknowledge the theft, even though they've posted on Twitter a few times since then. The organization had raised $2.5 million in pre-seed capital in June 2022.
- Tweet by CyversAlerts [archive]
- On-chain message from Kushagra Agarwal [archive]
Poloniex hacked for more than $120 million
Poloniex was initially tight-lipped, posting on Twitter that they had "disabled for maintenance" an exchange wallet. Justin Sun later updated that they were investigating the "hack incident", and promised to "fully reimburse" the massive theft... somehow. He later tweeted that they would offer a 5% "bounty" to the hacker if they returned the funds within a week, threatening to "engage law enforcement" otherwise.
CoinSpot exchange exploited
Wintermute declares friendship over with Near Foundation and Aurora Labs after they refuse to send $11 million
However, Near later decided it would not honor the redemption, accusing Wintermute of trying to pull off an arbitrage trade with the distressed asset. They also, somewhat curiously, claimed that the funds that were provided to Wintermute by the FTX estate may have been the tied to illegal activities. Aurora also described Wintermute's claims as "unfounded", and accused Wntermute of "tr[ying] to exploit the programme to profit from the purchase of distressed assets from the Alameda estate".
Wintermute has promised to "pursue all legal avenues" against the Near Foundation and Aurora Labs.